Over the past year the number of mobile applications that we have been pentesting are on the rise and it certainly seems that the future is going towards mobile technology. During the penetration testing one of the prerequisites that we faced was to “Root” the device in order to test certain local storage features and as well key features of an application. Rooting a device can turn out to be to a daunting task itself (am sure many of you would agree to this) especially if you are new to this field or if you are running the latest version of an operating system for e.g. A device running on Kitkat 4.4.2 and for many other such reasons it was turning out to be a difficult task.
Hence we at security theorem decided to get our hands dirty and find a way around this. And Taadaaaaa….. we certainly found a solution for this and we are happy to share this with the community. Below is a step by step guide on how to perform penetration testing without rooting:
Note: - Lot of applications these days have Mobile Device Management(MDM) systems built into them which check for the safety of the application if the device is “Rooted” or not. If the device is found to be “Rooted” then the application would not install/function properly. In such scenario this method of penetration testing becomes extremely useful and gives successful output.
- An Andriod device
- A Computer
- USB Cable
- Device Drivers installed on the pc
- ADB installed on the pc. ( if you do not have ADB you can find it at http://forum.xda-developers.com/showthread.php?t=1474956 )
- Andriod Backup Extractor (http://sourceforge.net/projects/adbextractor/files/ )
I hope now you have all the above things in place, so here we go :
Step-1
Connect the device to the computer & Turn on USB debugging from the device settings
Open Command prompt and type the following command : adb devices
If the device is correctly attached and drivers are installed then you shall see the result as above. The above image gives us a confirmation of our device being attached.
Step-2
In this step we shall find the package (Application) that we want to test.
Enter the command : adb shell pm list packages
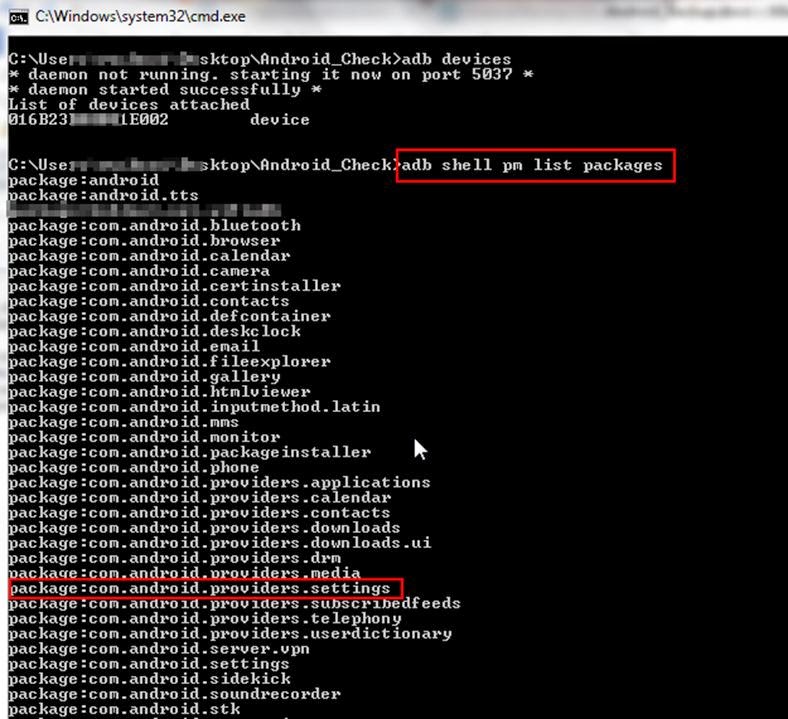
This will list all the applications that are installed on the device and from this list we can pick out desired package.
Step-3
Now backup the application that is needed to be tested
Enter the following command : adb backup -noapk com.android.providers.settings
It should be noted that “com.andriod.providers.settings ” has to be replaced by the name of the application which we want to test.
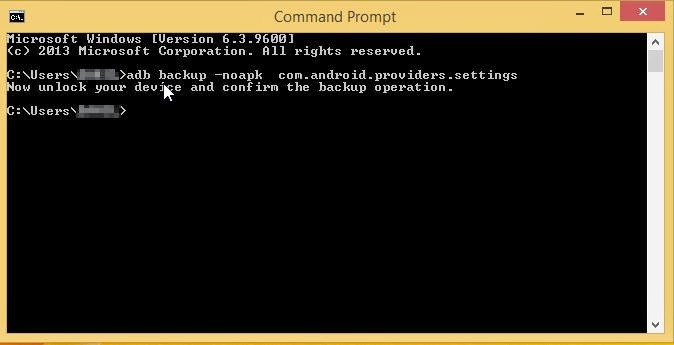
After the command the below screen will appear on your device. Select the option “Back up my data”
Here you can also backup your data in encrypted form by giving a password. The backup shall be created in the same directory with “.ab” extension.
Step-4
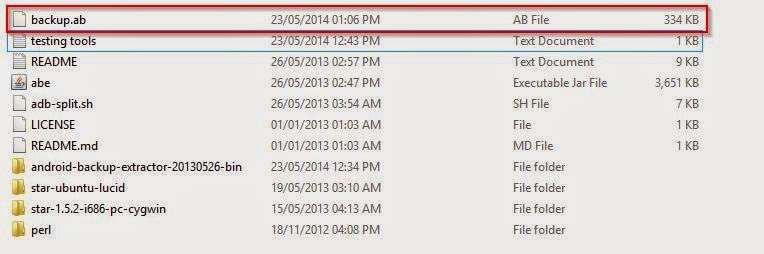
Now with the help of ADB extractor we shall extract our backup file.
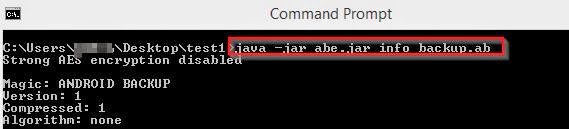
Apply the following command to the “backup.ab” file : java -jar abe.jar info backup.ab [password]
It should be noted that if a password was given at the time of backup it should be mentioned in the above command.
Step-5
The file which is now generated is not in readable format hence shall now unpack our backup file
Enter the following command : java -jar abe.jar unpack backup.ab backup.zip [password]
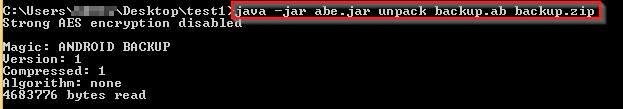
The image below shows the zip file being created.
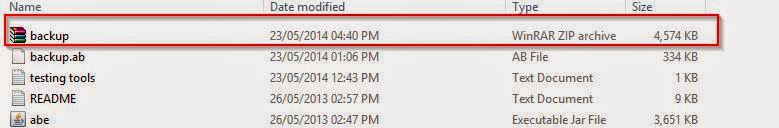
Now we can unzip the file to view it contents.
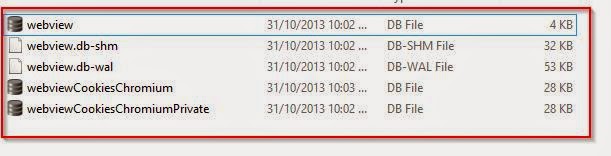
The images below show the content of the unzipped files.
These files can be analyzed through various pentesting tools such as sql lite browser.
In our next series of post we shall be talking about how to pentest an Iphone Application without jail breaking the device.
Hope you found this useful and you can leave your comments or suggests down below or you can reach us at info@securitytheorem.com for any queries.



Hello,
ReplyDeletei want to know that my HTC One S is not connecting with 3G Network, it remain stucks on 2G Network, Can you please tell me with using above trick or method to unlock it for 3G/4G Network ? this cell was released by T-Mobile,
Hello Anonymous,
ReplyDeleteThank you for going through our blog. Unfortunately what you are asking and what we have described work on two complete different concepts and we would recommend you contact your service provider to resolve the issue which you are facing.